The keys to successful ssi safety dashboards
ISS dashboards make life difficult for CISOs. From their design to their formatting, not forgetting the thorny subject of data collection. In this article, we give you the keys to successful SSI security dash boards. How do you choose the right indicators for your SSI dashboards? Which SSI indicators comply with the requirements of the standard or benchmark being monitored? Which tools should you choose to monitor the implementation of your SSIP? Discover our advice and a case study from the Haute Garonne department.

The keys to successful ssi safety dashboards
- Choosing the right indicators
- Meet the requirements of ISO and ANNSI standards
- Using the right tools to manage your PSSI
Why create SSI dashboards?
An SSI dashboard is an asset for improving the quality of security services. And thus control the overall level of information systems security. The implementation of an SSIP operational plan helps control the implementation of the SSIP. It enables :
- to fixed milestones, decide which measures are to be carried out, and communicate this;
- measure implementation progress. As such, it is not only a project monitoring tool for the SSI manager, but also a means of communicating with management.
How do you choose monitoring indicators for your SSI dashboards?
To ensure that objectives are met, it is important for CISOs to validate their expectations in terms of indicators with their management and business managers beforehand. The choice of indicators is not a trivial matter, and a balance must be struck between ease of use and usefulness.
It is recommended to build up a minimum portfolio of indicators, which will serve as a basic foundation. As a minimum, measurements should be collected on a quarterly basis, so that indicators can be calculated, analyzed and reported at the same frequency. Depending on the context of the organization, this may need to be modified. In any case, it is very useful to draw up a reference document describing the chosen indicators and how they are calculated.
Examples of indicators
- Tracking the number of employees trained
- Monitor changes in overall safety levels
- Vulnerability trends
- Measuring gaps between safety targets and actual performance
Know how to design SSI indicators that comply with the requirements of the standard or reference document being monitored
The ISO 27001 standard
To ensure the security of their sensitive information, organizations can rely on the ISO/IEC 27000 family of standards. ISO/IEC 27001 is the best-known cybersecurity standard in this family of a dozen or so. It defines a methodology for identifying cyber threats, controlling the risks associated with your organization's critical information, and implementing appropriate protection measures to ensure the confidentiality, availability and integrity of information.
The ISO 27004 standard
ISO 27004 provides best practices for assessing the effectiveness of your Information Security Management System (ISMS). The standard covers dashboards and indicators for effective ISMS management. These indicators and dashboards enable information systems management to establish a relationship between the target to be achieved (when setting up an ISMS) and the existing gaps in the company's current information system.
ANSSI
The ANSSI website provides an overview of digital security regulations relating to the protection of information systems, digital trust and, more specifically, cryptography and other technical regulations.
Example of SSI dashboards: Case study with the Haute Garonne department
CD31 shared its feedback on integrating the security component into digital transformation projects, at the CoTer Numérique. The department's general management was challenged by the cybersecurity figures. Indeed, since the start of the health crisis, 400% more cyber threats have been identified! To coordinate all the actions and projects arising from this information systems security policy, the local authority chose Project Monitor software. This project portfolio management software enables the implementation of dashboards, a veritable cockpit for the management of cybersecurity.
PSSI management tool: project portfolio management software Project Monitor
A tool to help CISOs manage their cybersecurity activities
A true cockpit for cybersecurity management, Project Monitor provides a 360° view. From global views, which can be integrated into reporting to top management, to operational views enabling rapid decisions on prioritized actions.
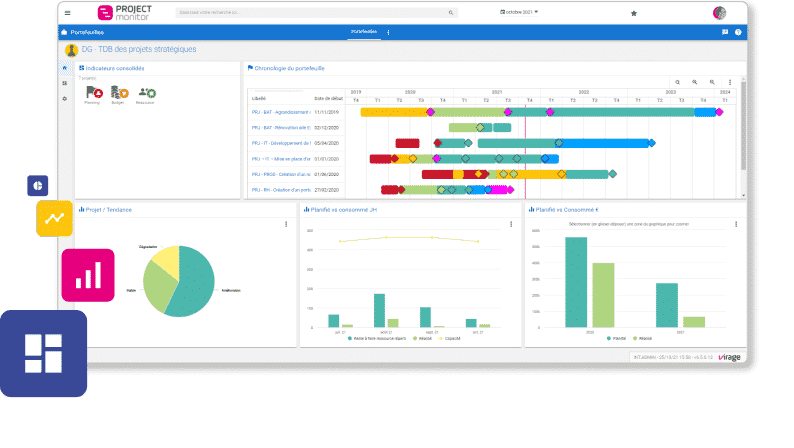
A key element in the CISO/management dialogue, Project Monitor 's SSI dashboards help to manage cybersecurity projects.
A 360° solution for IS project portfolio management
Facilitate the management of your project portfolio with a single software. Plan, manage, prioritize and visualize your project portfolio in just a few clicks. With Project MonitorYou will be able to track and organize your projects, regardless of their level of complexity. You will be able to track and organize your projects easily, regardless of their level of complexity
- Reporting
- Capacity schedule
- Time tracking
- Gantt
- Kanban
- Follow-up of IT requests
- Budget monitoring